Software Defined Networking
Software-defined networking (SDN) allows the separation of networks into a lower-level data plane and a higher-level control plane. The former performs the actual packet forwarding task whereas the latter allows centralized control and management for computer networks. This concept - originally from academia - gained additional support by industry, where SDN enables the development of innovative and radically new applications for users like data centers or Internet providers.
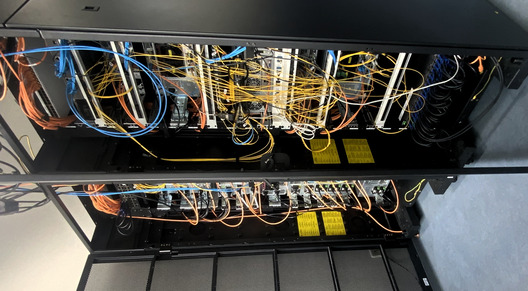
We apply SDN in different areas of our activity. One area is the development of new concepts that combine security and monitoring with systematic performance analysis of Virtual Network Functions (VNF) and Network Function Chaining (NFC). This includes measuring and modeling of virtualization technologies in NFC setups using network functions such as Firewalls, Load Balancing, or Deep Packet Inspection (DPI). Another area of research is the development of solutions for secure and scalable communication network infrastructures achieving cost-efficient, energy-efficient, reliable, and stable routing. These developments include flow-based network monitoring and network security applications. The design and development of an observational analysis system for the network’s backbone routing is also part of ongoing research. Core components are mechanisms allowing information fusion and classification for understanding the impact of SDN on backbone networks. For research purpose, the chair maintains its own testbed featuring SDN-enabled hardware and software as well as a toolset for high-speed traffic measurements. Utilizing this testbed allows us to investigate the feasibility of multicore systems for high-speed packet processing. Moreover, methods for performance evaluation and improvement of packet processing were developed, to gain an understanding of the interaction between various hardware and software components.
Formal Methods for SDN Security Administration (FM-SDN-SA)
One area of our SDN-related research is to apply formal methods for security administration of Software-Defined Networks. This work has been performed in part in connection the EU project EINS, the Network of Excellence on Internet Science. A huge part of a network's security depends on its configuration and administration. Network segmentation and isolation prevent unauthorized accesses and information leakage. It is a well-known fact in the area of firewalls that configuring and administrating network security policies is an error-prone process.
Our work focuses on two aspects: First, we provide tool support to understand existing, legacy network configurations and migrate them to SDN. Second, we develop methods to ease the inherent management complexity. Both aspects focus on tool support and automation to prevent human error. It is important not to replace human error with errors in our tools; consequently, all our methods are machine-verifiable proven correct with the Isabelle/HOL theorem prover. Aspect one: It is important to understand existing, legacy network configuration before a network can be migrated to SDN. We focus one specific technology: Linux/netfilter iptables. The iptables firewall is wide-spread, real-world approved, and supports many features. Consequently, there are numerous configurations which utilize a vast amount of features, and as many deployments exist for a long time, many configurations are no longer fully understood by their administrator(s). We have collected many such configurations and developed scientific methods to understand challenging configurations. These methods have a large potential to be applied to other SDN-related network technologies. We provide a formal semantics for iptables packet filtering. Given those formal foundations, we provide tools to check BCP 38 and visualize the network access control policies implied by a firewall. Current work includes translating iptables and routing configuration to the Open vSwitch in a fully automated and fully machine-verified manner. Aspect two: Managing access control policies by hand scales quadratically with the number of (logical) network participants. Consequently, managing access control policies by hand is error prone. We have shown that even advanced administrators may make errors for policies with only ten hosts. To conquer this complexity challenge, we provide management methods on higher abstraction layers. We have presented a full toolchain to automatically translate network security invariants to Open vSwitch and iptables configurations. Those high-level security invariants directly encode the scenario-specific security requirements, are modular and composable, and can be securely auto-completed. Consequently, managing security invariants instead of low-level access control policies removes inherent complexity and can thus prevent human error. In addition, our tool can give feedback about the specified invariants and verify existing configurations – e.g. obtained by (aspect one) – against such invariants.
Scientists: Eric Hauser, Stefan Lachnit, M.Sc., Prof. Dr.-Ing. Georg Carle, Manuel Simon, M.Sc., Sebastian Gallenmüller, Henning Stubbe, Kilian Holzinger
Projects: HYPERNIC, AI4Performance, SENDATE, I2RS, SASER, EINS, SecFuNet
Publications
| 2025-12-01 | Stefan Lachnit, Sebastian Gallenmüller, Eric Hauser, Florian Wiedner, Kilian Holzinger, Henning Stubbe, Thomas Senftl, Georg Carle, “MoonEm — High-Precision Path Property Emulation Using DPDK,” Proc. ACM Netw., vol. 3, no. CoNEXT4, Dec. 2025. [Url] [Pdf] [DOI] [Bib] |
| 2025-06-01 | Manuel Simon, Sebastian Warter, Sebastian Gallenmüller, Georg Carle, “TEE Time at P4—Performance Analysis of Trusted Execution Environments for Packet Processing,” in 2025 11th IEEE International Conference on Network Softwarization (NetSoft), Jun. 2025, pp. 348–352. [Pdf] [Preprint] [Slides] [DOI] [Bib] |
| 2025-06-01 | Florian Wiedner, Dominik Kreutzer, Jonas Andre, Georg Carle, “Continuous Integration for Networks Supporting Low-Latency Using Hybrid Network Emulation,” in 2025 36rd International Teletraffic Congress (ITC-36), Jun. 2025. [Pdf] [Homepage] [Bib] |
| 2025-06-01 | Marcel Kempf, Simon Tietz, Benedikt Jaeger, Johannes Späth, Georg Carle, Johannes Zirngibl, “QUIC Steps: Evaluating Pacing Strategies in QUIC Implementations,” Proc. ACM Netw., vol. 3, no. CoNEXT2, Jun. 2025. [Url] [Pdf] [Homepage] [DOI] [Bib] |
| 2025-04-01 | Manuel Simon, Sebastian Gallenmüller, Georg Carle, “Dynamic Data Planes Updates using Lua and libmoon,” in 4th GI/ITG KuVS Fachgespräch "Network Softwarization", Apr. 2025. [Pdf] [Preprint] [Slides] [DOI] [Bib] |
| 2025-01-01 | Stefan Genchev, Lars Wüstrich, Georg Carle, “Attestation of Electronic Identification Schemes Based on Secure Channels Through Security Microcontrollers,” in Availability, Reliability and Security, Cham, 2025, pp. 75–92. [Bib] |
| 2024-12-01 | Johannes Späth, Max Helm, Benedikt Jaeger, Georg Carle, “Sim2HW: Modeling Latency Offset Between Network Simulations and Hardware Measurements,” in Proceedings of the 3rd GNNet Workshop: Graph Neural Networking Workshop (GNNet ’24), Los Angeles, CA, USA, Dec. 2024. [Pdf] [Slides] [Homepage] [Rawdata] [DOI] [Bib] |
| 2024-10-01 | Manuel Simon, Sebastian Gallenmüller, Georg Carle, “On-the-fly Table Insertions on Programmable Software Data Planes,” in 20th International Conference on Network and Service Management (CNSM 2024), Prague, Czech Republic, Oct. 2024. [Pdf] [Preprint] [Slides] [DOI] [Bib] |
| 2024-09-01 | Henning Stubbe, Sebastian Gallenmüller, Manuel Simon, Eric Hauser, Dominik Scholz, Georg Carle, “Exploring data plane updates on P4 switches with P4Runtime,” Computer Communications, vol. 225, pp. 44–53, Sep. 2024. [Url] [Pdf] [DOI] [Bib] |
| 2024-08-01 | Manuel Simon, Henning Stubbe, Sebastian Gallenmüller, Georg Carle, “Honey for the Ice Bear - Dynamic eBPF in P4,” in Proceedings of the ACM SIGCOMM 2024 Workshop on EBPF and Kernel Extensions, Sydney, NSW, Australia, Aug. 2024, pp. 44–50. [Url] [Pdf] [Preprint] [Slides] [Sourcecode] [DOI] [Bib] |
| 2024-05-01 | Lars Wüstrich, Sebastian Gallenmüller, Stephan Günther, Georg Carle, Marc-Oliver Pahl, “Shells Bells: Cyber-Physical Anomaly Detection in Data Centers,” in 2024 IEEE/IFIP Network Operations and Management Symposium (NOMS 2024), Seoul, Korea, May 2024. [Pdf] [Bib] |
| 2024-05-01 | Markus Sosnowski, Patrick Sattler, Johannes Zirngibl, Tim Betzer, Georg Carle, “Propagating Threat Scores With a TLS Ecosystem Graph Model Derived by Active Measurements,” in Proc. Network Traffic Measurement and Analysis Conference (TMA), May 2024. [Pdf] [Slides] [Homepage] [DOI] [Bib] |
| 2024-01-01 | Henning Stubbe, Sebastian Gallenmüller, Georg Carle, “The pos Experiment Controller: Reproducible & Portable Network Experiments,” in 2024 19th Wireless On-Demand Network Systems and Services Conference (WONS), 2024, pp. 1–8. [Pdf] [Preprint] [DOI] [Bib] |
| 2023-12-01 | Patrick Sattler, Johannes Zirngibl, Mattijs Jonker, Oliver Gasser, Georg Carle, Ralph Holz, “Packed to the Brim: Investigating the Impact of Highly Responsive Prefixes on Internet-wide Measurement Campaigns,” Proc. ACM Netw., vol. 1, no. CoNEXT3, Dec. 2023. [Url] [Pdf] [Homepage] [DOI] [Bib] |
| 2023-06-01 | Manuel Simon, Sebastian Gallenmüller, Georg Carle, “Never Miss Twice - Add-On-Miss Table Updates in Software Data Planes,” in KuVS Fachgespräch - Würzburg Workshop on Modeling, Analysis and Simulation of Next-Generation Communication Networks 2023 (WueWoWAS’23), Würzburg, Germany, Jun. 2023, p. 5. Best Workshop Contribution [Pdf] [Preprint] [Slides] [DOI] [Bib] |
| 2021-06-01 | Peter Okelmann, Leonardo Linguaglossa, Fabien Geyer, Paul Emmerich, Georg Carle, “Adaptive Batching for Fast Packet Processing in Software Routers using Machine Learning,” in Proceedings of the 7th IEEE International Conference on Network Softwarization, Jun. 2021. [Pdf] [Sourcecode] [Bib] |
| 2020-06-01 | Maximilian Pudelko, Paul Emmerich, Sebastian Gallenmüller, Georg Carle, “Performance Analysis of VPN Gateways,” in IFIP Networking 2020, Paris, France, Jun. 2020. [Pdf] [Bib] |
| 2019-12-01 | Charles Shelbourne, Leonardo Linguaglossa, Aldo Lipani, Tianzhu Zhang, Fabien Geyer, “On the Learnability of Software Router Performance via CPU Measurements,” in Proceedings of the 2019 CoNEXT Student Workshop, Orlando, USA, Dec. 2019. [Pdf] [Rawdata] [DOI] [Bib] |
| 2019-06-01 | Leonardo Linguaglossa, Fabien Geyer, Wenqin Shao, Frank Brockners, Georg Carle, “Demonstrating the Cost of Collecting In-Network Measurements for High-Speed VNFs,” in IFIP TMA Demo, Paris, France, Jun. 2019. [Pdf] [DOI] [Bib] |
| 2019-05-01 | Benedikt Jaeger, Dominik Scholz, Daniel Raumer, Fabien Geyer, Georg Carle, “Reproducible Measurements of TCP BBR Congestion Control,” Computer Communications, vol. 144, pp. 31–43, May 2019. [Pdf] [DOI] [Bib] |
| 2019-05-01 | Fabien Geyer, Stefan Schmid, “DeepMPLS: Fast Analysis of MPLS Configurations Using Deep Learning,” in Proceedings of the 18th International IFIP TC6 Networking Conference, Warsaw, Poland, May 2019. [Pdf] [Slides] [Sourcecode] [Rawdata] [DOI] [Bib] |
| 2019-04-01 | Fabien Geyer, Steffen Bondorf, “DeepTMA: Predicting Effective Contention Models for Network Calculus using Graph Neural Networks,” in Proceedings of the 38th IEEE International Conference on Computer Communications (INFOCOM 2019), Paris, France, Apr. 2019. [Pdf] [Rawdata] [DOI] [Bib] |
| 2018-12-01 | Cornelius Diekmann, Johannes Naab, Andreas Korsten, Georg Carle, “Agile Network Access Control in the Container Age,” IEEE Transactions on Network and Service Management, Dec. 2018. [Pdf] [DOI] [Bib] |
| 2018-10-01 | Paul Emmerich, Maximilian Pudelko, Quirin Scheitle, Georg Carle, “Efficient Dynamic Flow Tracking for Packet Analyzers,” in CloudNet, Tokyo, Japan, Oct. 2018. [Pdf] [Bib] |
| 2018-09-01 | Dominik Scholz, Daniel Raumer, Paul Emmerich, Alexander Kurtz, Krzysztof Lesiak, Georg Carle, “Performance Implications of Packet Filtering with Linux eBPF,” in Teletraffic Congress (ITC 30), 2018 30th International, Vienna, Austria, Sep. 2018. [Pdf] [Slides] [Bib] |
| 2018-05-01 | Dominik Scholz, Benedikt Jaeger, Lukas Schwaighofer, Daniel Raumer, Fabien Geyer, Georg Carle, “Towards a Deeper Understanding of TCP BBR Congestion Control,” in IFIP Networking 2018, Zurich, Switzerland, May 2018. [Pdf] [Sourcecode] [DOI] [Bib] |
| 2017-07-01 | Paul Emmerich, Daniel Raumer, Sebastian Gallenmüller, Florian Wohlfart, Georg Carle, “Throughput and Latency of Virtual Switching with Open vSwitch: A Quantitative Analysis,” Journal of Network and Systems Management, Jul. 2017. [Pdf] [DOI] [Bib] |
| 2017-06-01 | Paul Emmerich, Maximilian Pudelko, Sebastian Gallenmüller, Georg Carle, “FlowScope: Efficient Packet Capture and Storage in 100 Gbit/s Networks,” in IFIP Networking 2017, Stockholm, Sweden, Jun. 2017. [Pdf] [Bib] |
| 2016-10-01 | Julius Michaelis, Cornelius Diekmann, “LOFT – Verified Migration of Linux Firewalls to SDN,” Archive of Formal Proofs, Oct. 2016. Formal proof development [Url] [Bib] |
| 2016-09-01 | Cornelius Diekmann, Lars Hupel, “Iptables_Semantics,” Archive of Formal Proofs, Sep. 2016. Formal proof development [Url] [Bib] |
| 2016-08-01 | Julius Michaelis, Cornelius Diekmann, “Routing,” Archive of Formal Proofs, Aug. 2016. Formal proof development [Url] [Bib] |
| 2016-08-01 | Cornelius Diekmann, Julius Michaelis, Max Haslbeck, “Simple Firewall,” Archive of Formal Proofs, Aug. 2016. Formal proof development [Url] [Bib] |
| 2016-06-01 | Cornelius Diekmann, Julius Michaelis, Lars Hupel, “IP Addresses,” Archive of Formal Proofs, Jun. 2016. Formal proof development [Url] [Bib] |
| 2016-01-01 | Dario Banfi, Olivier Mehani, Guillaume Jourjon, Lukas Schwaighofer, Ralph Holz, “Endpoint-transparent multipath transport with software-defined networks,” in 41st IEEE Conference on Local Computer Networks (LCN), 2016. [Pdf] [Bib] |
| 2015-11-01 | Cornelius Diekmann, Lukas Schwaighofer, Georg Carle, “Certifying Spoofing-Protection of Firewalls,” in 11th International Conference on Network and Service Management, CNSM, Barcelona, Spain, Nov. 2015. [Url] [Preprint] [Sourcecode] [Rawdata] [DOI] [Bib] |
| 2015-11-01 | Cornelius Diekmann, Andreas Korsten, Georg Carle, “Demonstrating topoS: Theorem-Prover-Based Synthesis of Secure Network Configurations,” in 2nd International Workshop on Management of SDN and NFV Systems, manSDN/NFV, Barcelona, Spain, Nov. 2015. [Url] [Preprint] [Slides] [Sourcecode] [DOI] [Bib] |
| 2015-11-01 | Stanislav Lange, Anh Nguyen-Ngoc, Steffen Gebert, Thomas Zinner, Michael Jarschel, Andreas Koepsel, Marc S. Clos, Daniel Raumer, Sebastian Gallenmüller, Georg Carle, Phuoc Tran-Gia, “Performance Benchmarking of an LTE SGW,” in 2nd International Workshop on Management of SDN and NFV Systems 2015, Nov. 2015. [Pdf] [Bib] |
| 2015-10-01 | Paul Emmerich, Sebastian Gallenmüller, Daniel Raumer, Florian Wohlfart, Georg Carle, “MoonGen: A Scriptable High-Speed Packet Generator,” in Internet Measurement Conference (IMC) 2015, IRTF Applied Networking Research Prize 2017, Tokyo, Japan, Oct. 2015. [Pdf] [Bib] |
| 2015-06-01 | Cornelius Diekmann, Lars Hupel, Georg Carle, “Semantics-Preserving Simplification of Real-World Firewall Rule Sets,” in 20th International Symposium on Formal Methods, Jun. 2015, pp. 195–212. [Url] [Preprint] [Slides] [Sourcecode] [Rawdata] [DOI] [Bib] |
| 2015-06-01 | Viktor Goldberg, Florian Wohlfart, Daniel Raumer, “Datacenter Network Virtualization in Multi-Tenant Environments,” in 8. DFN-Forum Kommunikationstechnologien, Jun. 2015. [Pdf] [Bib] |
| 2015-05-01 | Sebastian Gallenmüller, Paul Emmerich, Florian Wohlfart, Daniel Raumer, Georg Carle, “Comparison of Frameworks for High-Performance Packet IO,” in ACM/IEEE Symposium on Architectures for Networking and Communications Systems (ANCS 2015), Oakland, CA, USA, May 2015. [Pdf] [Bib] |
| 2015-05-01 | Sebastian Gallenmüller, Paul Emmerich, Daniel Raumer, Georg Carle, “MoonGen: Software Packet Generation for 10 Gbit and Beyond,” in 12th USENIX Symposium on Networked Systems Design and Implementation (NSDI 15), Oakland, CA, USA, May 2015. [Pdf] [Poster] [Bib] |
| 2015-04-01 | Paul Emmerich, Daniel Raumer, Florian Wohlfart, Georg Carle, “Assessing Soft- and Hardware Bottlenecks in PC-based Packet Forwarding Systems,” in Fourteenth International Conference on Networks (ICN 2015), Best Paper Award, Barcelona, Spain, Apr. 2015. [Pdf] [Bib] |
| 2015-03-01 | Alexander Beifuß, Daniel Raumer, Paul Emmerich, Torsten M. Runge, Florian Wohlfart, Bernd E. Wolfinger, Georg Carle, “A Study of Networking Software Induced Latency,” in 2nd International Conference on Networked Systems 2015 (NetSys’15), Cottbus, Germany, Mar. 2015. [Pdf] [Bib] |
| 2015-01-01 | Syed Naveed Rizvi, Daniel Raumer, Florian Wohlfart, Georg Carle, “Towards Carrier Grade SDNs,” Journal of Computer Networks, 2015. [Pdf] [Bib] |
| 2014-12-01 | Paul Emmerich, Daniel Raumer, Florian Wohlfart, Georg Carle, “A Study of Network Stack Latency for Game Servers,” in 13th Annual Workshop on Network and Systems Support for Games (NetGames’14), Nagoya, Japan, Dec. 2014. [Pdf] [Bib] |
| 2014-10-01 | Paul Emmerich, Daniel Raumer, Florian Wohlfart, Georg Carle, “Performance Characteristics of Virtual Switching,” in 2014 IEEE 3rd International Conference on Cloud Networking (CloudNet’14), Luxembourg, Oct. 2014. [Pdf] [Bib] |
| 2014-09-01 | Diego Kreutz, Eduardo Feitosa, Hugo Cunha, Heiko Niedermayer, Holger Kinkelin, “Increasing the Resilience and Trustworthiness of OpenID Identity Providers for Future Networks and Services,” in Ninth International Conference on Availability, Reliability and Security (ARES), Sep. 2014, pp. 317–324. [Bib] |
| 2014-09-01 | Daniel Raumer, Lukas Schwaighofer, Georg Carle, “MonSamp: A Distributed SDN Application for QoS Monitoring,” in Proceedings of the Federated Conference on Computer Science and Information Systems (FedCSIS’14), 1st Workshop on Software-Defined Networking, Warsaw, Poland, Sep. 2014. [Pdf] [Bib] |
| 2014-05-01 | Cornelius Diekmann, Lars Hupel, Georg Carle, “Directed Security Policies: A Stateful Network Implementation,” in Engineering Safety and Security Systems, Singapore, May 2014, vol. 150, pp. 20–34. [Url] [Pdf] [Preprint] [Slides] [Sourcecode] [DOI] [Bib] |
| 2013-05-01 | Lothar Braun, Cornelius Diekmann, Nils Kammenhuber, Georg Carle, “Adaptive Load-Aware Sampling for Network Monitoring on Multicore Commodity Hardware,” in IFIP Networking 2013, New York, NY, May 2013. [Url] [Pdf] [Preprint] [Sourcecode] [Bib] |
